
AD FS 2.0 Service Communication Certificate Lost
Ran into this today when trying to troubleshoot why our AD FS 2.0 instance was not working. Basically, through a series of events the certificate that was being used as the service communication certificate in AD FS 2.0 became expired. Then it was deleted out of the computer store completely.
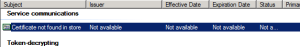
When this happens AD FS 2.0 shows this in the GUI.
In addition, you also get a nice error with an “Object not set to an instance of an object” when you click on “Set Service Communications Certificate” if you are following the instructions from the Technet Wiki or the Technet Article itself.
So how do we resolve this? Powershell to the rescue.
First, you can verify that this is your problem.
Load the Powershell addon for AD FS and then use the get-adfscertificate command.
1 2 | add-pssnapin microsoft.adfs.powershell get-adfscertificate | ? { $_.CertificateType -eq "Service-Communications" } |
Certificate    : CertificateType : Service-Communications IsPrimary      : True StoreLocation  : LocalMachine StoreName      : My
Notice that the “Certificate” is null. This is what is likely killing the AD FS 2.0 Management Console.
Now we just need to assign it a new certificate, in the same Powershell window. Note that you will need the certificate thumbprint of the certificate that you have already added to the computer personal store. This is typically the same certificate used to secure your IIS site. See the Technet documentation for those requirements.
Make sure that the user running your AD FS 2.0 Windows Service (ours was running as Network Service), has permissions to the private key of the certificate you are using. You can give read access through the certificates snap-in.
1 | set-adfscertificate -certificatetype "Service-Communications" -thumprint "Your Certificate Thumbprint" |
Once this is done, you will need to bounce the AD FS 2.0 windows service on each server in the farm, and then you will see the proper certificate noted in the GUI after you refresh.
Now everything should work as expected.
One response to “AD FS 2.0 Service Communication Certificate Lost”
Leave a Reply
You must be logged in to post a comment.





You missed the “b” in thumbprint but otherwise worked flawlessly! Thanks!